Overview
- This book is open access, which means that you have free and unlimited access
- For persons engaged with modern computing environments and cyber-physical systems
- This book fills the gap between software management paradigms and cybersecurity models
- Provides a comprehensive review of the main concepts, architectures, algorithms, and non-technical aspects
Part of the book series: Lecture Notes in Computer Science (LNCS, volume 13300)
Buy print copy
Tax calculation will be finalised at checkout
About this book
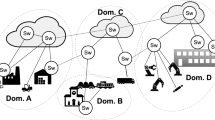
This open access book presents the main scientific results from the H2020 GUARD project. The GUARD project aims at filling the current technological gap between software management paradigms and cybersecurity models, the latter still lacking orchestration and agility to effectively address the dynamicity of the former. This book provides a comprehensive review of the main concepts, architectures, algorithms, and non-technical aspects developed during three years of investigation; the description of the Smart Mobility use case developed at the end of the project gives a practical example of how the GUARD platform and related technologies can be deployed in practical scenarios.
We expect the book to be interesting for the broad group of researchers, engineers, and professionals daily experiencing the inadequacy of outdated cybersecurity models for modern computing environments and cyber-physical systems.Similar content being viewed by others
Keywords
- cloud computing
- computer crime
- computer networks
- computer security
- cryptography
- cyber security
- data communication systems
- data flow architectures
- data management systems
- data security
- electromagnetic interference and compatibility
- general programming languages
- health informatics
- intrusion detection
- network protocols
- network security
- network simulations
- sensors and actuators
- signal processing
- telecommunication traffic
Table of contents (10 chapters)
-
Front Matter
-
Back Matter
Editors and Affiliations
Bibliographic Information
Book Title: Cybersecurity of Digital Service Chains
Book Subtitle: Challenges, Methodologies, and Tools
Editors: Joanna Kołodziej, Matteo Repetto, Armend Duzha
Series Title: Lecture Notes in Computer Science
DOI: https://doi.org/10.1007/978-3-031-04036-8
Publisher: Springer Cham
eBook Packages: Computer Science, Computer Science (R0)
Copyright Information: The Editor(s) (if applicable) and The Author(s) 2022
Softcover ISBN: 978-3-031-04035-1Published: 07 April 2022
eBook ISBN: 978-3-031-04036-8Published: 06 April 2022
Series ISSN: 0302-9743
Series E-ISSN: 1611-3349
Edition Number: 1
Number of Pages: XI, 257
Number of Illustrations: 19 b/w illustrations, 71 illustrations in colour
Topics: Computer Communication Networks, Legal Aspects of Computing, Security, Information Systems Applications (incl. Internet)



